[ad_1]
A recent report from security researchers at FortiGuard Labs – Fortinet published their findings regarding a new variant of Ransoware that infects itself to devices under the guise of Critical Windows Updates.
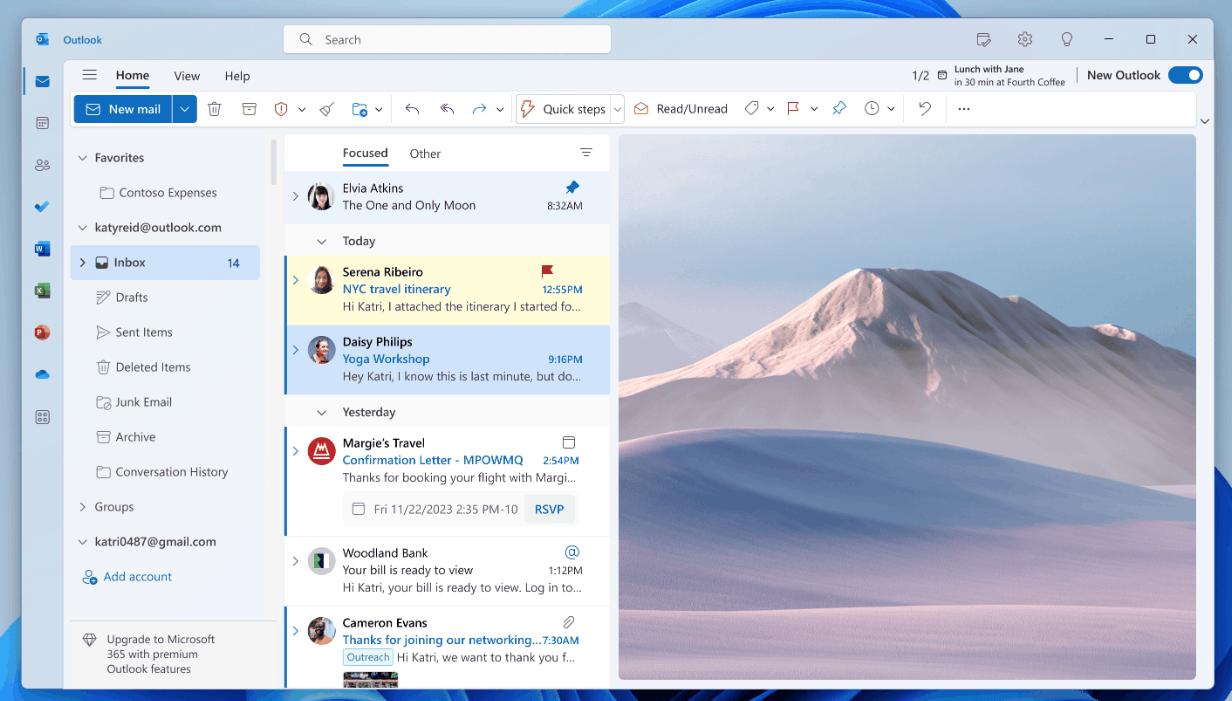
As in the picture above, the ransomware nicknamed “Big Head” will basically encrypt files in the background while the user is waiting for this fake Windows update process. Interestingly this process only takes about 30 seconds.
In addition, there is another variant that uses files powershell named “cry.ps1” to encrypt the compromised system.
After quite a buzz, Trend Micro also published its own research and findings regarding Big Head a few days ago where they revealed more details about the malware, where it turns out that Big Head will check virtual environments like Virtual Box / VMWare and even remove backup volume shadong copy service or VSS which makes this ransomware quite scary. And here is a statement from Trend Micro:
"he ransomware checks for strings like VBOX, Virtual, or VMware in the disk enumeration registry to determine whether the system is operating within a virtual environment. It also scans for processes that contain the following substring: VBox, prl_(parallel’s desktop), srvc.exe, vmtoolsd.
The malware identifies specific process names associated with virtualization software to determine if the system is running in a virtualized environment, allowing it to adjust its actions accordingly for better success or evasion. It can also proceed to delete recovery backup available by using the following command line:
vssadmin delete shadows /all /quiet & bcdedit.exe /set {default} recoveryenabled no & bcdedit.exe /set {default} bootstatuspolicy ignoreallfailures"
Now to get information about how it works, and other things, you can read the technical details from Trend Micro on the page following.
So with that, users are expected to be careful when installing something because apart from Big Head, of course there are still lots of ransomware and other malware that are dangerous and threaten user data.
via: TrendMicro, Neowin
[ad_2]
Source link